Beyond Signatures: How Machine Learning and Autonomous Agents Are Reshaping Intrusion Detection
Introduction
For decades, intrusion detection systems (IDS) have relied on a simple yet effective strategy: matching network traffic against a database of known attack signatures. This approach works well against predictable threats, but modern adversaries constantly evolve their tactics, leaving signature-based systems blind to novel or obfuscated attacks. A new wave of intelligent detection methods is now emerging, powered by machine learning and autonomous agents. These technologies fundamentally change the core question of intrusion detection, moving from "Does this match a known pattern?" to "Does this actually make sense in context?" This shift promises greater accuracy, adaptability, and resilience against advanced cyber threats.
The Limitations of Signature-Based Detection
Signature-based IDS, such as Snort in its traditional mode, operate by comparing traffic to predefined rules. Each rule describes a known malicious pattern—a specific byte sequence, packet header anomaly, or command structure. This method is computationally efficient and easy to deploy, but it carries inherent weaknesses:
- Blindness to zero-day exploits: Attackers who use never-before-seen techniques can bypass detection until a signature is created.
- Evasion through obfuscation: Simple variations in packet payloads, such as alternate character encodings or fragment reassembly tricks, often cause signature matches to fail.
- High false positive rates in dynamic environments: Rules optimized for one network may trigger alerts on benign traffic in another, overwhelming security teams.
- Maintenance burden: Security analysts must constantly update signature databases and tune rules to keep pace with emerging threats.
These shortcomings highlight the need for a detection paradigm that understands not just what a packet looks like, but what it means within the context of normal network behavior.
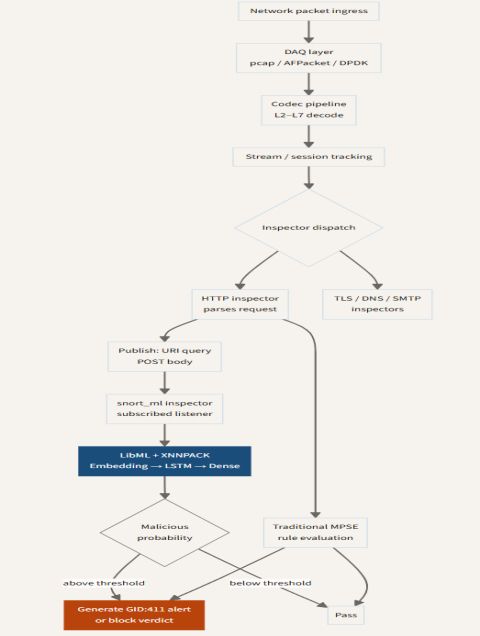
How SnortML Brings Machine Learning to the Table
SnortML extends Snort's capabilities by integrating machine learning models directly into the detection pipeline. Instead of relying solely on static signatures, SnortML trains classifiers on historical network data, enabling the system to identify anomalies and malicious patterns that do not match any known rule. Key features include:
- Contextual analysis: ML models evaluate packet sequences, time deltas, and session metadata to detect deviations from baseline behavior.
- Adaptive thresholds: The system automatically adjusts sensitivity based on observed traffic patterns, reducing false positives while maintaining high detection rates.
- Hybrid detection: SnortML can combine signature matching with ML-based scoring, so known attacks are caught quickly while subtle anomalies are flagged for further investigation.
By raising the detection question from "Is this a known pattern?" to "Does this make sense in the current context?", SnortML enhances the robustness of intrusion detection without requiring a complete overhaul of existing infrastructure.
The Rise of Agentic AI in Security
Machine learning models, while powerful, still require human oversight to adjust parameters, investigate anomalies, and decide on responses. The next evolution in intrusion detection involves agentic AI—autonomous software entities capable of perceiving their environment, making decisions, and taking actions without direct human intervention.
Autonomous Decision-Making
Agentic AI systems go beyond simple anomaly detection. They can triage alerts, correlate events across multiple sensors, and even initiate containment measures—such as blocking a suspicious IP address or isolating a compromised host—based on learned policies. This reduces the time between detection and response, a critical factor in limiting damage from fast-moving attacks.
Contextual Understanding
These agents maintain a model of the network state, including user roles, application dependencies, and typical traffic flows. When assessing whether a request is legitimate, they consider not just the packet content but also the broader operational context. For example, an agent might allow a remote login attempt during business hours from a known administrator's device, while flagging the same attempt from an unrecognized source at 3 AM as suspicious.
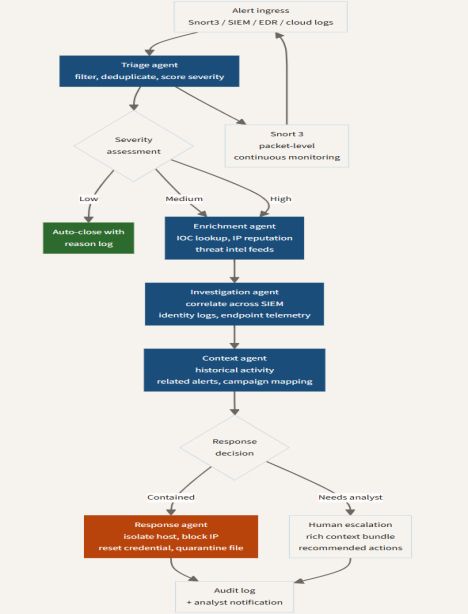
Collaborative Intelligence
Agentic AI also enables collaboration between multiple detection nodes. Agents can share insights, update each other on emerging threats, and coordinate defensive actions across distributed environments. This creates a self-organizing security ecosystem that adapts to threats in real time.
The Evolving Architecture of Intrusion Detection
The integration of machine learning and autonomous agents is not merely an add-on to signature-based systems; it represents a fundamental architectural shift. Modern intrusion detection frameworks are moving toward a layered approach:
- Layer 1: Signature matching for high‑confidence, low‑latency detection of known attacks.
- Layer 2: Machine learning for anomaly detection and identification of novel threats in context.
- Layer 3: Agentic AI for autonomous triage, correlation, and response.
This layered architecture retains the speed of traditional methods while adding the flexibility and intelligence needed to combat advanced adversaries. As mentioned earlier, the central question shifts from "Does this match?" to "Does this make sense?", enabling security teams to focus on genuine incidents rather than noise.
Challenges and Considerations
Despite their promise, ML‑based and agentic systems introduce new challenges:
- Data quality and bias: Models trained on incomplete or skewed network data may produce unreliable results.
- Explainability: Understanding why an ML model flagged a particular packet can be difficult, complicating incident investigation.
- Adversarial attacks: Sophisticated attackers may craft inputs specifically designed to evade machine learning models.
- Resource requirements: Real‑time inference requires significant computational power, potentially straining hardware.
Addressing these issues requires ongoing research, robust testing, and careful deployment practices.
Conclusion
Intrusion detection is undergoing a profound transformation. By moving beyond static signatures and embracing machine learning and autonomous agents, security systems can now evaluate traffic based on context rather than mere pattern matching. Tools like SnortML exemplify how hybrid approaches combine the best of both worlds, while agentic AI promises to automate decision‑making and response. As the cyber threat landscape continues to evolve, this shift from "Does it match?" to "Does it make sense?" will be essential for defending tomorrow's networks.
Related Articles
- 10 Key Insights into NVIDIA and ServiceNow's Autonomous AI Agent Collaboration
- Pixel 11: 10 Crucial Rumors and Concerns You Should Know About
- Startup's Cab-Less Autonomous Delivery Bot Stuns Haulage Industry
- How to Run a Prepersonalization Workshop That Sets Your Team Up for Personalization Success
- Vacuum Giant Dreame Unveils Modular Smartphone Plans at California Event
- Q&A: Energizer's Safer Coin Batteries Explained
- Founders warned: 'The business didn't need more of me, it needed a different me' – Why stepping aside can save a growing company
- Apple's Next Wearable: A Camera-Equipped Pendant and Smart Glasses