How to Implement a Defense-in-Depth Security Architecture for Agentic Workflows in CI/CD Pipelines
Introduction
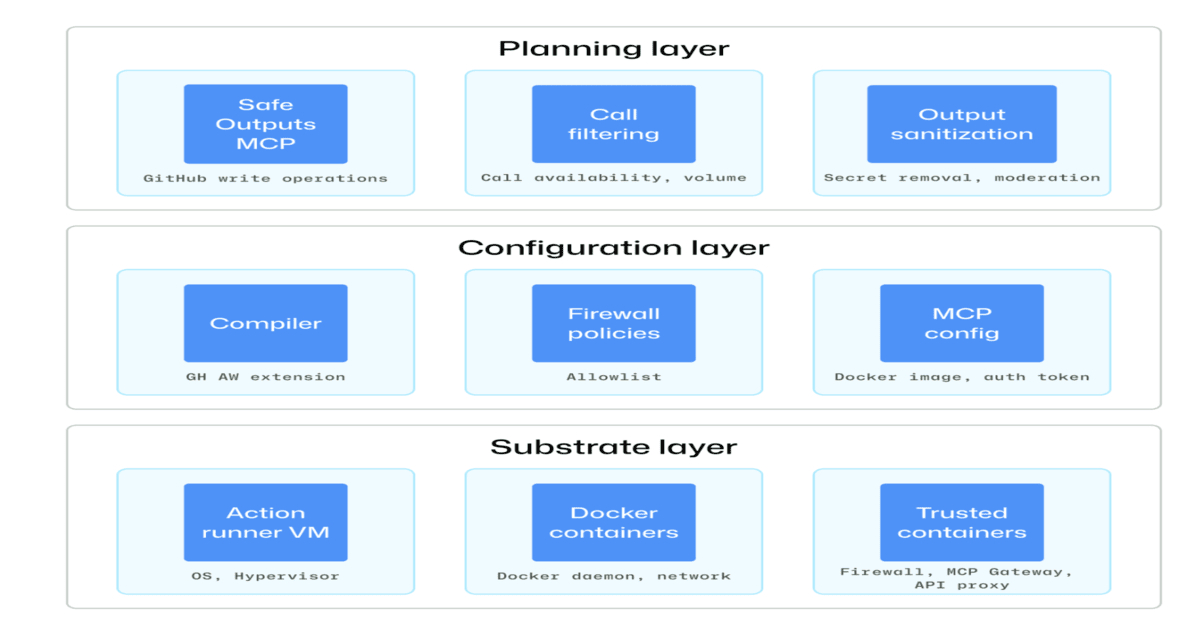
As autonomous AI agents become more integrated into modern CI/CD pipelines, they bring immense efficiency—but also new security risks. Prompt injection, privilege escalation, and unintended actions can compromise your entire deployment chain. To safely harness these agents, you need a defense-in-depth security architecture like the one GitHub has outlined. This guide walks you through building such a system, focusing on isolation, constrained execution, and auditability. By the end, you’ll have a step-by-step plan to secure your agentic workflows.
What You Need
- A CI/CD platform (e.g., GitHub Actions, GitLab CI, Jenkins) that supports custom runners or virtual environments
- Basic understanding of agentic workflows and how they interact with your pipeline (e.g., AI agents that generate code, review PRs, or trigger deployments)
- Access to containerization or virtualization technologies (Docker, Kubernetes, or cloud sandbox services)
- Role-based access control (RBAC) and secrets management tools (e.g., GitHub Secrets, HashiCorp Vault)
- Logging and monitoring infrastructure (e.g., SIEM, audit trails, or cloud-native logging)
- Knowledge of least-privilege principles: aim to grant only the minimum permissions necessary
Step-by-Step Guide
Step 1: Map Your Agentic Workflow’s Attack Surface
Before adding security controls, understand where attacks can occur. Document every point where an autonomous agent interacts with your pipeline:
- Which inputs does the agent receive? (e.g., code changes, user prompts, repository metadata)
- Which actions can the agent perform? (e.g., write to repositories, merge PRs, run scripts, access secrets)
- Which external systems does it call? (e.g., databases, cloud APIs, third-party services)
Identify risks such as prompt injection (where an attacker manipulates the agent’s instructions), privilege escalation (agent gaining unintended access), and unintended actions (e.g., the agent triggering a destructive deployment). This threat model is the foundation of your defense.
Step 2: Isolate Agent Execution in Sandboxed Environments
The cornerstone of GitHub’s approach is isolation. Run every agent action inside a sandboxed environment that is ephemeral and disposable. Use containers (e.g., Docker) or virtual machines:
- Define a custom runner or job environment that starts fresh for each agent call.
- Restrict network access: only allow connections to explicitly whitelisted services.
- Mount only necessary filesystems as read-only, and never expose the host system.
- Set resource limits (CPU, memory, disk) to prevent resource exhaustion attacks.
For example, in GitHub Actions, create a reusable workflow that spins up a Docker container with --read-only and --cap-drop=ALL. This ensures that even if an agent is compromised, it can’t persist beyond the session.
Step 3: Enforce Constrained Execution through Minimal Permissions
Agents should never have more permissions than they need for a single task. Follow the principle of least privilege:
- Create dedicated service accounts or tokens for agent actions, scoped to the absolute minimum (e.g., only read access to a specific repo, or write access to a temporary branch).
- Use OIDC or federated identities to issue short-lived credentials that expire after the workflow completes.
- Restrict which actions the agent can call (e.g., in GitHub Actions, limit to
actions/checkoutand a few custom actions). - Implement gate checks: require human approval before any agent-triggered deployment or destructive operation.
GitHub’s architecture uses “restricted permissions” to prevent privilege escalation. For instance, if an agent only needs to generate code suggestions, it should not have permissions to merge PRs or write to the main branch.
/presentations/game-vr-flat-screens/en/smallimage/thumbnail-1775637585504.jpg)
Step 4: Implement Full Execution Traceability
To detect and recover from incidents, you need complete auditability. Log every action an agent takes, including:
- Input prompts and outputs
- System calls, network connections, file modifications
- Timestamps, agent identity, and session IDs
Use structured logging and forward logs to a centralized audit trail (e.g., SIEM, AWS CloudTrail, or GitHub’s audit log for Actions). Ensure logs are immutable and tamper-proof. Also, record the why: what triggered each agent action? This traceability allows you to replay an incident and understand its root cause.
Step 5: Integrate Pre- and Post-Execution Checks
Add automated security checks before and after each agent action:
- Pre-execution: Validate agent inputs against known malicious patterns (e.g., prompt injection regexes). Use a content filter or a security scanner to reject suspicious prompts.
- Post-execution: Analyze agent outputs for signs of compromise, such as unexpected API calls, file writes outside allowed paths, or attempts to read secrets.
These checks can be built as custom actions or integrated with existing security tools like Semgrep, Checkov, or GitHub’s Dependabot. Consider a feedback loop: if a check fails, automatically revoke the agent’s session and alert the security team.
Step 6: Monitor and Continuously Improve
Security is not a one-time setup. Set up real-time monitoring dashboards that track:
- Number of agent executions and failure rates
- Exceptions or security alerts triggered
- Anomalous behaviors (e.g., unusual network destinations, high resource consumption)
Periodically review your threat model and update your sandbox configurations, permissions, and audit rules. Run red-team exercises to test your defenses. Emulate attack scenarios like prompt injection and see if your isolation holds.
Tips for Success
- Start small: Pilot your defense architecture on a single, non-critical agent before rolling out across your entire CI/CD.
- Use open standards: Leverage OIDC for authentication and OPA (Open Policy Agent) for fine-grained policy decisions.
- Educate your team: Make sure developers understand the risks of agentic workflows and how to avoid writing prompts that leak secrets.
- Keep agents stateless: Stateless agents are easier to sandbox and recover from failures.
- Document everything: Maintain clear runbooks for incident response when an agent is compromised.
- Stay updated: Follow GitHub’s security advisories and updates to their Actions ecosystem for new defenses.
Related Articles
- Homebridge 2.0 Adds Matter Support: Expanding Apple Home Compatibility
- Uber's Bold New Plan: Turning Drivers into a Real-Time Sensor Network for Autonomous Vehicles
- How to Seize an Enemy Position Using Only Unmanned Systems: A Step-by-Step Guide
- 6 Steps to Ignite Your Personalization Engine: The Prepersonalization Workshop Guide
- Dreame Unveils Smartphones Amid Skepticism: Modular Aurora Nex LS1 Raises Eyebrows
- Q&A: Industrial Automation Threat Landscape in Q4 2025 – Trends and Key Threats
- Pixel 11 Rumors Spark Concerns: Downgrades Alongside New Camera Tech
- 7 Creative DIY Peripherals to Supercharge Your Desktop